AI Attacks Move at Machine Speed. We Need More Time.
Our existing defences still work. What’s changed is the job they now have to do.
The headlines about Claude Mythos have been striking. An AI that can complete a 32-step corporate network attack simulation end-to-end. A model finding new software vulnerabilities in codebases that survived decades of expert review. If you work in security, or just follow the technology closely, it would be easy to read those stories and conclude that it’s game over. That the attackers have won. That nothing we build can hold.
That conclusion is wrong. And I think it’s worth being direct about that, because the doomer framing is both inaccurate and genuinely harmful. It leads organisations to fatalism when what the moment actually calls for is action.
What frontier AI changes is speed. Not the fundamental nature of how network attacks work, but the velocity at which they happen. A human attacker moving manually through a network, probing systems, identifying high-value targets, escalating access, used to take hours. CrowdStrike’s 2026 Global Threat Report records the average time between initial access and an attacker moving to high-value targets elsewhere in the network at 29 minutes. The fastest recorded case in 2025 was 27 seconds.
The security controls we already have haven’t stopped working. What’s changed is the job they’re now being asked to do.
When the attacker was human, layered security controls were designed to create enough friction that they’d just give up and move to an easier target. An isolated network segment, an account with limited privileges, a system requiring explicit authentication: none of these are impenetrable, but together they made the effort not worth it. That logic still applies. Against an autonomous AI agent, the same controls serve a different purpose: not to make the attacker give up, but to slow a machine-speed attack down enough that human defenders have a chance to respond.
That shift in purpose, from deterrence to delay, is the entire argument of this article. The long-term answer to machine-speed attacks is machine-speed defence, and that tooling is developing. In the meantime, the architecture we already know how to build is more important than it has ever been.
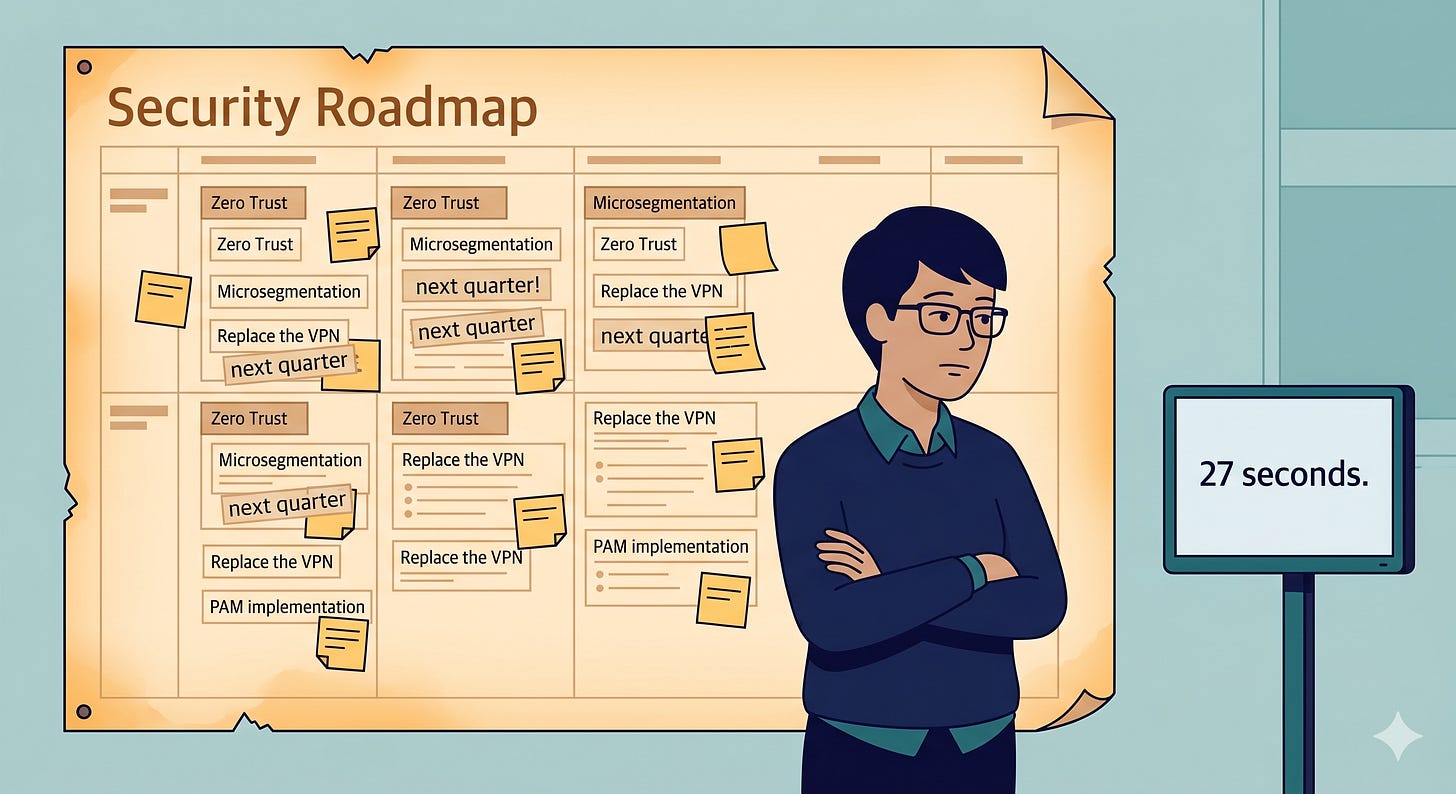
Zero Trust is not a new concept. “Never trust, always verify”, the idea that no user, device, or system should be implicitly trusted just because it’s inside the network, has been the theoretical gold standard for enterprise security for years. Microsegmentation, application control, privileged access management, replacing legacy VPN with more granular access tools: these have been on roadmaps, in strategy documents, and in conference presentations for most of the last decade.
They’re also genuinely hard to implement. That’s not a criticism of anyone. Legacy infrastructure makes this difficult, with application dependencies that are complex and often poorly documented. Microsegmentation projects, which divide a network into smaller isolated zones so a breach in one can’t spread freely to others, require buy-in across teams that don’t always collaborate: network teams, application owners, security, operations. Privileged access management done properly touches every system in the estate. Replacing a VPN means retiring infrastructure that works, in favour of something new, with all the business friction that entails.
Gartner’s 2025 Market Guide estimates that fewer than 5% of enterprises pursuing Zero Trust have implemented microsegmentation. That’s not negligence. It’s a rational response to a cost-benefit calculation that, until recently, made the complexity hard to justify.
Those barriers haven’t disappeared. But the risk of not acting is moving into a different category. When the threat model assumed a human attacker moving at human speed, a detect-and-respond model could work, you had time, and good monitoring could compensate for imperfect architecture. When the attacker is an autonomous AI agent, the enforcement has to be built in. Detection and response are still essential, but they need something to buy them time.
These controls won’t stop a determined AI-powered attack indefinitely. but that’s not the job. They slow machine-speed attacks down to something human defenders can detect and respond to, by removing the paths of least resistance that autonomous agents depend on.
Microsegmentation
82% of intrusions in 2025 required no malware at all, attackers moved through networks using stolen credentials and legitimate tools, exploiting the fact that most enterprise networks let a compromised system reach adjacent ones freely. Microsegmentation removes that open floor plan: the network is divided into isolated zones, and every connection between them requires explicit authorisation. An agent that breaches one endpoint finds itself contained, unable to reach the next system without a policy that specifically permits it.
Privileged Access Management
Palo Alto’s 2025 research found that 66% of social engineering attacks specifically target privileged accounts, the admin credentials that can access any system, because an attacker who obtains them has, in practical terms, already won. PAM changes that by eliminating standing privileges: elevated access is granted just-in-time for a specific task and expires, so a stolen credential carries no power until someone explicitly requests it. The same principle needs to extend to machine identities, service accounts, API keys, automation scripts, which now outnumber human identities 82 to 1 and are almost entirely unmanaged.
Managed Endpoints and Session Hygiene
Infostealers processed 51.7 million packages of stolen credentials in 2025, up 72% year on year, and what makes them particularly dangerous is that they capture live session tokens, the authenticated state a browser holds to keep you logged in, which allows an attacker to bypass two-factor authentication entirely without ever knowing your password. The primary source of exposure is unmanaged devices: personal laptops and AI assistants running in the same browser session as authenticated work applications, invisible to IT and ungoverned by any security policy. Managed browser profiles, conditional access policies, and short session lifetimes won’t eliminate the risk, but they shrink the window of usefulness for any token that is stolen.
Replacing Legacy VPN
A traditional VPN grants network-level access on authentication, once through the tunnel, an attacker has a ticket to the internal network that an autonomous agent will explore at machine speed. ZTNA replaces that model: instead of connecting to the network, you connect to specific applications for specific sessions, with every request evaluated in real time against identity, device posture, and context. The broader network is never exposed, which removes the open terrain that lateral movement depends on.
Everything above addresses AI as an external attacker. There’s a second threat that’s emerging faster than most organisations have absorbed.
Gartner projects that 40% of enterprise applications will incorporate AI agents by the end of 2026. Meeting recorders. Document processors. Automated research tools. Copilot integrations accessing your files, emails, and calendars. These agents are trusted, always on, and increasingly have access to sensitive internal data.
The attack is called prompt injection: an adversary embeds malicious instructions inside content the agent will process, an email, a shared document, a webpage it’s asked to summarise, and the agent acts on them as if they were legitimate. A meeting recorder becomes a surveillance tool; a document assistant becomes an exfiltration channel; and because the agent is trusted and its actions appear authorised, the security architecture designed for human users doesn’t catch it.
Extending least-privilege principles to AI agents, giving them access only to what they specifically need, for only as long as they need it, with full audit trails, is the control that most organisations haven’t implemented, and most haven’t even formally defined. It’s also where I think the next significant wave of enterprise breaches is going to originate. I’ll be writing about this in more depth soon.
The long-term answer to machine-speed attacks is machine-speed defence, AI-assisted detection, automated containment, continuous verification at a pace no human team can match. That tooling is coming, but it isn’t here yet.
Which means the question for every security leader right now isn’t whether to pursue Zero Trust. It’s which controls to prioritise first, in which order, starting this quarter. PAM and Microsegmentation deliver the most containment value against autonomous lateral movement. Start there. The complexity hasn’t disappeared, but the calculus has shifted for good.
Zero Trust was always the right architecture. It just took autonomous AI to make the argument impossible to defer.
I write about AI, cybersecurity, and technology every Friday. Subscribe to get it in your inbox.
Sources & Further Reading
AISI (UK AI Security Institute) — Our evaluation of Claude Mythos Preview’s cyber capabilities. aisi.gov.uk
CrowdStrike — 2026 Global Threat Report. crowdstrike.com
Palo Alto Networks — Unit 42 2025 Global Incident Response Report. paloaltonetworks.com
Constella Intelligence — 2026 Identity Breach Report. constella.ai
HP Wolf Security — Tracing the Rise of Breaches Involving Session Cookie Theft. threatresearch.ext.hp.com (December 2025)
Anthropic — Misuse reporting / AWS Security Blog, February 2026. anthropic.com
Gartner — Market Guide for Network Security Microsegmentation, 2025. gartner.com
Palo Alto Networks — 2026 Predictions for Autonomous AI. paloaltonetworks.com/blog